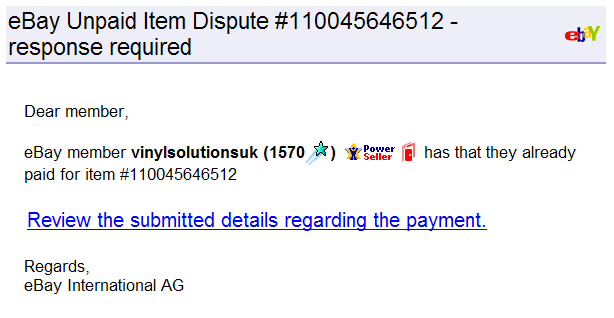
Generally I delete phishing emails without a second glance, but this one caught my eye for being so realistic, and using a interesting method intended for accessibility to disguise a fraudulent link.
I do have an ebay account, but I haven’t bought or sold anything through it for yonks, so it seems unlikely to be real. It also is not personalised, which ebay and paypal tend to do, but even so, it appears very realistic, I have a de-fanged version for viewing. It contains several links, all but one were to the real ebay (but in my version go through to a local page).
Each of the images appear real, and infact are taken from one of ebay’s servers, e.g:
http://pics.ebaystatic.com/aw/pics/email/eBayLogo.gifWhen you mouse-over the main link, the one that is crying out to be clicked, it even appears to link to:
http://www.ebay.comIn my email client (Thunderbird) which uses the Gecko rendering engine, the link does actually go to ebay.com, so why did they bother sending it? Well, using Internet Explorer 6 or 7 (and therefore I would assume Outlook or Outlook Express), clicking the link takes you somewhere else.
The email firstly hides an emty link with an ID attribute:
<P><A id=SPOOF href="ebay_fake.html"></A></P>Then it uses a label that targets that ID:
<LABEL for=SPOOF>
<U style="CURSOR: pointer; COLOR: blue">
Review the submitted details
regarding the payment.</U>
</LABEL>In most browsers the link works, in IE the label works. Presumably because in IE labels & accesskeys go stright to the link specified, whereas other browsers require another keypress, so the actual link is followed rather than the IDed one. If you were curious, the domain linked to was pelvired.be, but the link doesn’t work anymore.
Any ideas as to whether this is a bug or a feature?
Technorati Tags: